A mannequin context protocol (MCP) device can declare to execute a benign job comparable to “validate e-mail addresses,” but when the device is compromised, it may be redirected to satisfy ulterior motives, comparable to exfiltrating your whole deal with ebook to an exterior server. Conventional safety scanners might flag suspicious community calls or harmful capabilities and pattern-based detection might determine identified threats, however neither functionality can join a semantic and behavioral mismatch between what a device claims to do (e-mail validation) and what it truly does (exfiltrate information).
Introducing behavioral code scanning: the place safety evaluation meets AI
Addressing this hole requires rethinking how safety evaluation works. For years, static utility safety testing (SAST) instruments have excelled at discovering patterns, tracing dataflows, and figuring out identified menace signatures, however they’ve at all times struggled with context. Answering questions like, “Is a community name malicious or anticipated?” and “Is that this file entry a menace or a characteristic?” requires semantic understanding that rule-based methods can’t present. Whereas giant language fashions (LLMs) deliver highly effective reasoning capabilities, they lack the precision of formal program evaluation. This implies they’ll miss delicate dataflow paths, wrestle with complicated management buildings, and hallucinate connections that don’t exist within the code.
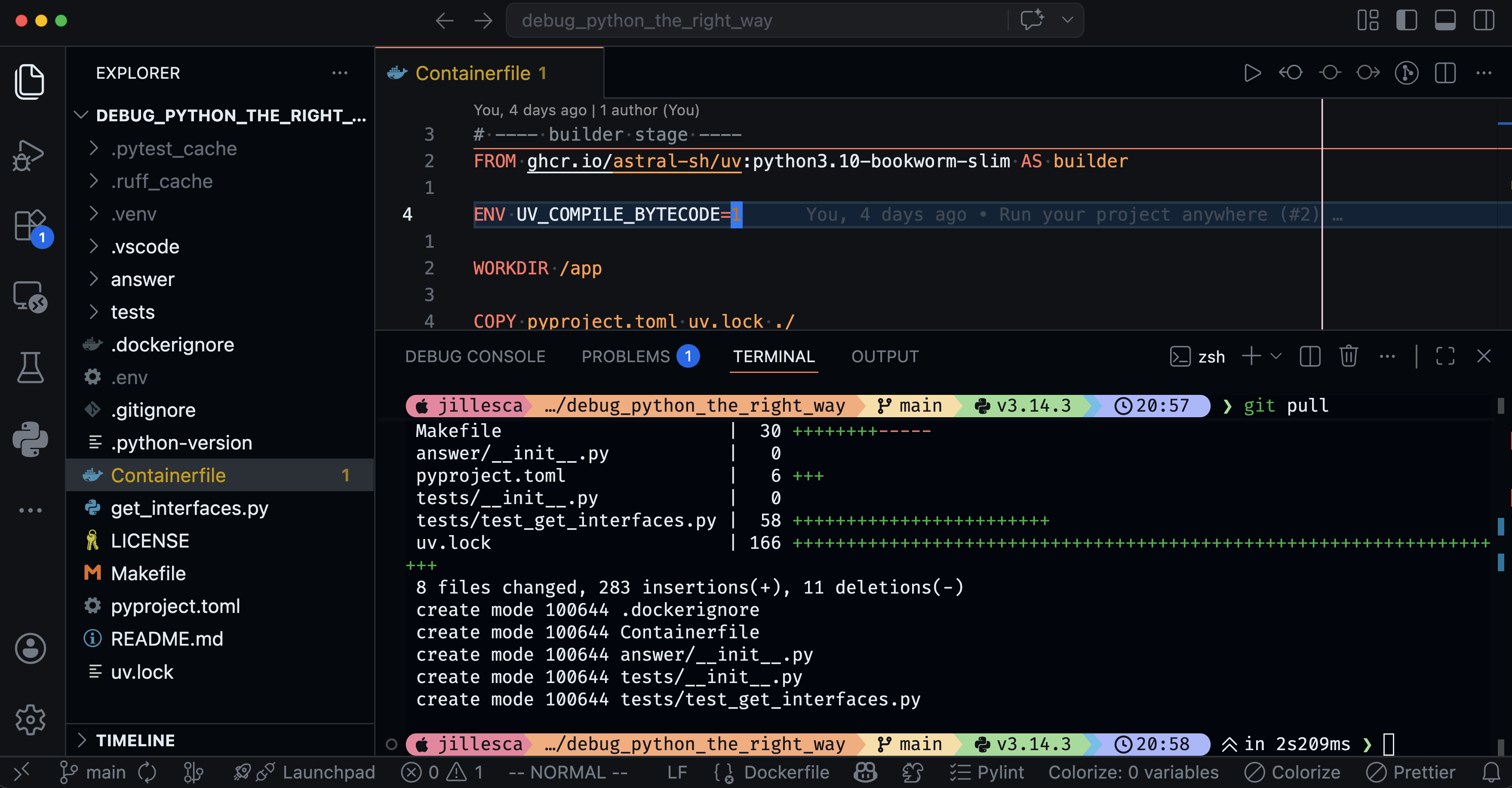
The answer is in combining each: rigorous static evaluation capabilities that feed exact proof to LLMs for semantic evaluation. It delivers each the precision to hint precise information paths, in addition to the contextual judgment to judge whether or not these paths symbolize official conduct or hidden threats. We applied this in our behavioral code scanning functionality into our open supply MCP Scanner.
Deep static evaluation armed with an alignment layer
Our behavioral code scanning functionality is grounded in rigorous, language-aware program evaluation. We parse the MCP server code into its structural elements and use interprocedural dataflow evaluation to trace how information strikes throughout capabilities and modules, together with utility code, the place malicious conduct usually hides. By treating all device parameters as untrusted, we map their ahead and reverse flows to detect when seemingly benign inputs attain delicate operations like exterior community calls. Cross-file dependency monitoring then builds full name graphs to uncover multi-layer conduct chains, surfacing hidden or oblique paths that might allow malicious exercise.
In contrast to conventional SAST, our method makes use of AI to match a device’s documented intent towards its precise conduct. After extracting detailed behavioral alerts from the code, the mannequin seems for mismatches and flags instances the place operations (comparable to community calls or information flows) don’t align with what the documentation claims. As a substitute of merely figuring out harmful capabilities, it asks whether or not the implementation matches its said function, whether or not undocumented behaviors exist, whether or not information flows are undisclosed, and whether or not security-relevant actions are being glossed over. By combining rigorous static evaluation with AI reasoning, we will hint precise information paths and consider whether or not these paths violate the device’s said function.
Bolster your defensive arsenal: what behavioral scanning detects
Our improved MCP Scanner device can seize a number of classes of threats that conventional instruments miss:
Hidden Operations: Undocumented community calls, file writes, or system instructions that contradict a device’s said function. For instance, a device claiming to help with sending emails that secretly bcc’s all of your emails to an exterior server. This compromise truly occurred, and our behavioral code scanning would have flagged it.
Knowledge Exfiltration: Instruments that carry out their said operate appropriately whereas silently copying delicate information to exterior endpoints. Whereas the consumer receives the anticipated end result; an attacker additionally will get a replica of that information.
Injection Assaults: Unsafe dealing with of consumer enter that allows command injection, code execution, or related exploits. This consists of instruments that move parameters straight into shell instructions or evaluators with out correct sanitization.
Privilege Abuse: Instruments that carry out actions past their said scope by accessing delicate assets, altering system configurations, or performing privileged operations with out disclosure or authorization.
Deceptive Security Claims: Instruments that assert that they’re “protected,” “sanitized,” or “validated” whereas missing the protections and making a harmful false assurance.
Cross-boundary Deception: Instruments that seem clear however delegate to helper capabilities the place the malicious conduct truly happens. With out interprocedural evaluation, these points would evade surface-level assessment.
Why this issues for enterprise AI: the menace panorama is ever rising
In the event you’re deploying (or planning to deploy) AI brokers in manufacturing, contemplate the menace panorama to tell your safety technique and agentic deployments:
Belief selections are automated: When an agent selects a device primarily based on its description, that’s a belief determination made by software program, not a human. If descriptions are deceptive or malicious, brokers may be manipulated.
Blast radius scales with adoption: A compromised MCP device doesn’t have an effect on a single job, it impacts each agent invocation that makes use of it. Relying on the device, this has the potential to affect methods throughout your whole group.
Provide chain threat is compounding: Public MCP registries proceed to increase, and improvement groups will undertake instruments as simply as they undertake packages, usually with out auditing each implementation.
Guide assessment processes miss semantic violations: Code assessment catches apparent points, however distinguishing between official and malicious use of capabilities is tough to determine at scale.
Integration and deployment
We designed behavioral code scanning to combine seamlessly into current safety workflows. Whether or not you’re evaluating a single device or scanning a whole listing of MCP servers, the method is straightforward and the insights are actionable.
CI/CD pipelines: Run scans as a part of your construct pipeline. Severity ranges assist gating selections, and structured outputs allows programmatic integration.
A number of output codecs: Select concise summaries for CI/CD, detailed reviews for safety opinions, or structured JSON for programmatic consumption.
Black-box and white-box protection: When supply code isn’t obtainable, customers can depend on current engines comparable to YARA, LLM-based evaluation, or API scanning. When supply code is obtainable, behavioral scanning offers deeper, evidence-driven evaluation.
Versatile AI ecosystem assist: Suitable with main LLM platforms so you possibly can deploy in alignment together with your safety and compliance necessities
A part of Cisco’s dedication to AI safety
Behavioral code scanning strengthens Cisco’s complete method to AI safety. As a part of the MCP Scanner toolkit, it enhances current capabilities whereas additionally addressing semantic threats that disguise in plain sight. Securing AI brokers requires the assist of instruments which can be purpose-built for the distinctive challenges of agentic methods.
When paired with Cisco AI Protection, organizations acquire end-to-end safety for his or her AI functions: from provide chain validation and algorithmic pink teaming to runtime guardrails and steady monitoring. Behavioral code scanning provides a important pre-deployment verification layer that catches threats earlier than they attain manufacturing.
Behavioral code scanning is obtainable as we speak in MCP Scanner, Cisco’s open supply toolkit for securing MCP servers, giving organizations a sensible to validate the instruments their brokers rely on.
For extra on Cisco’s complete AI safety method, together with runtime safety and algorithmic pink teaming, go to cisco.com/ai-defense.